“The only certain thing about IT security is that nothing is certain.” As organizations rely more on information technology and information systems to do business, the digital risk threat landscape expands, exposing ecosystems to new critical vulnerabilities. Risk assessments are nothing new and whether you like it or not, you are in the risk management […]
What is Cybersecurity Awareness Training? Cybersecurity awareness training is a program designed to educate individuals, including your staff, about the various cyber threats and risks that exist in the digital world. It aims to provide them with the knowledge and skills necessary to identify and avoid these threats, as well as to respond appropriately if […]
When a breach happens on the Internet, it’s important to know ASAP so that you can double-check it hasn’t been used against the client already. Proactively protect Your Business from stolen credentials Dark web monitoring is a process of searching for and monitoring information found on the dark web. It finds stolen or leaked information, […]
Managed Cybersecurity is a comprehensive cybersecurity solution powered by Aegisys. It provides businesses with a proactive cybersecurity a-la-carte approach to managing and protecting their digital assets from cyber threats. Here are a few reasons why Aegisys Managed Cybersecurity is beneficial: Expertise: Aegisys has a team of experienced cybersecurity professionals who are well-versed in the latest […]
Duo Multi-Factor Authentication by Cisco DUO MFA is recommended to keep your employee logins secure and optimized for productivity. Multi-Factor Authentication (MFA) is an authentication method that requires the user to provide two or more verification factors to gain access to a resource such as an application, online account, or a VPN. MFA is a […]
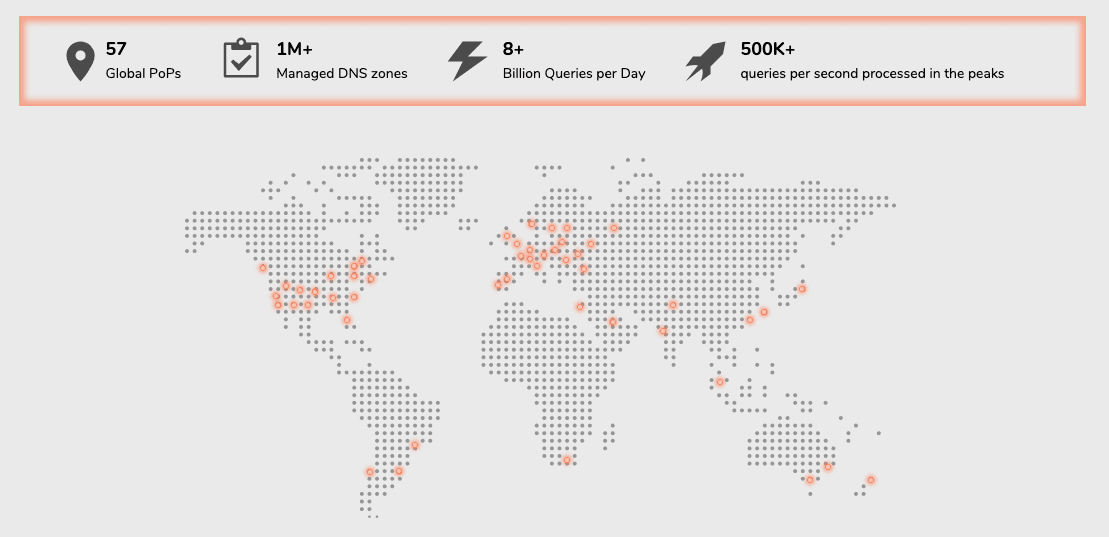
Aegisys DNS services come with a wide variety of security features built-in, including DNSSEC, DDoS mitigation, multi-DNS functionality, and load balancing. What is DNS security? DNS security is the practice of protecting DNS infrastructure from cyber attacks in order to keep it performing quickly and reliably. An effective DNS security strategy incorporates a number of overlapping […]
Hackers Don’t Sleep. Neither Does vPenTest. If your organization was targeted tomorrow, would you be prepared? Let’s work together and find out. See what a hacker sees on your network before they do. Aegisys vPenTest is essentially a hacker on a company’s network. It looks for sensitive data, performs exploits, conducts man-in-the-middle attacks, crack […]
Get Bitdefender Endpoint Protection to secure your business against Ransomware and Malware.
Get the Aegisys RAPID RESPONSE Protection layer of Premium Endpoint Protection & Response (EDR & MDR + SOC)